Cybersecurity Project: Epic Games Store Packet Capture - IPs 1
Last time, we took a look a number of suspicious domains captured in network traffic to a sandboxed Epic Games Store installation.
To progress the investigation, we're going to look a number of IP addresses for the following domain: account-public-service-prod03.ol.epicgames.com
This was a particularly interesting domain for analysis, due to two past malware detections:
Sep 19, 2021 8e7c791dd2a860fb8ff4630b4079351d9865c73316d3071664a8cab86737e890 TEL:Trojan:Win64/GoCLR.MR!MTB
Aug 31, 2019 b81db9595e7cdc16ca6f106f5610e4442cbaf9049940938b34ce759a42688dfa Win32:BackdoorX-gen\ [Trj] Win.Trojan.Tofsee-6840338-0 Backdoor:Win32/Tofsee.T
Figuring Out the IP
The first step of the process is figuring out which IP associated with the domain was actually being used. There were 22 IP addresses associated with the domain, and unless EGS decided to bounce between them all during the process, only one was in use.
This required me to go through the list of IPs until I finally found the one IP that was utilized for the connection, which took a decent amount of time due to the size of my packet capture.
Luckily, I found it on the fourth attempt - 52.205.83.9.
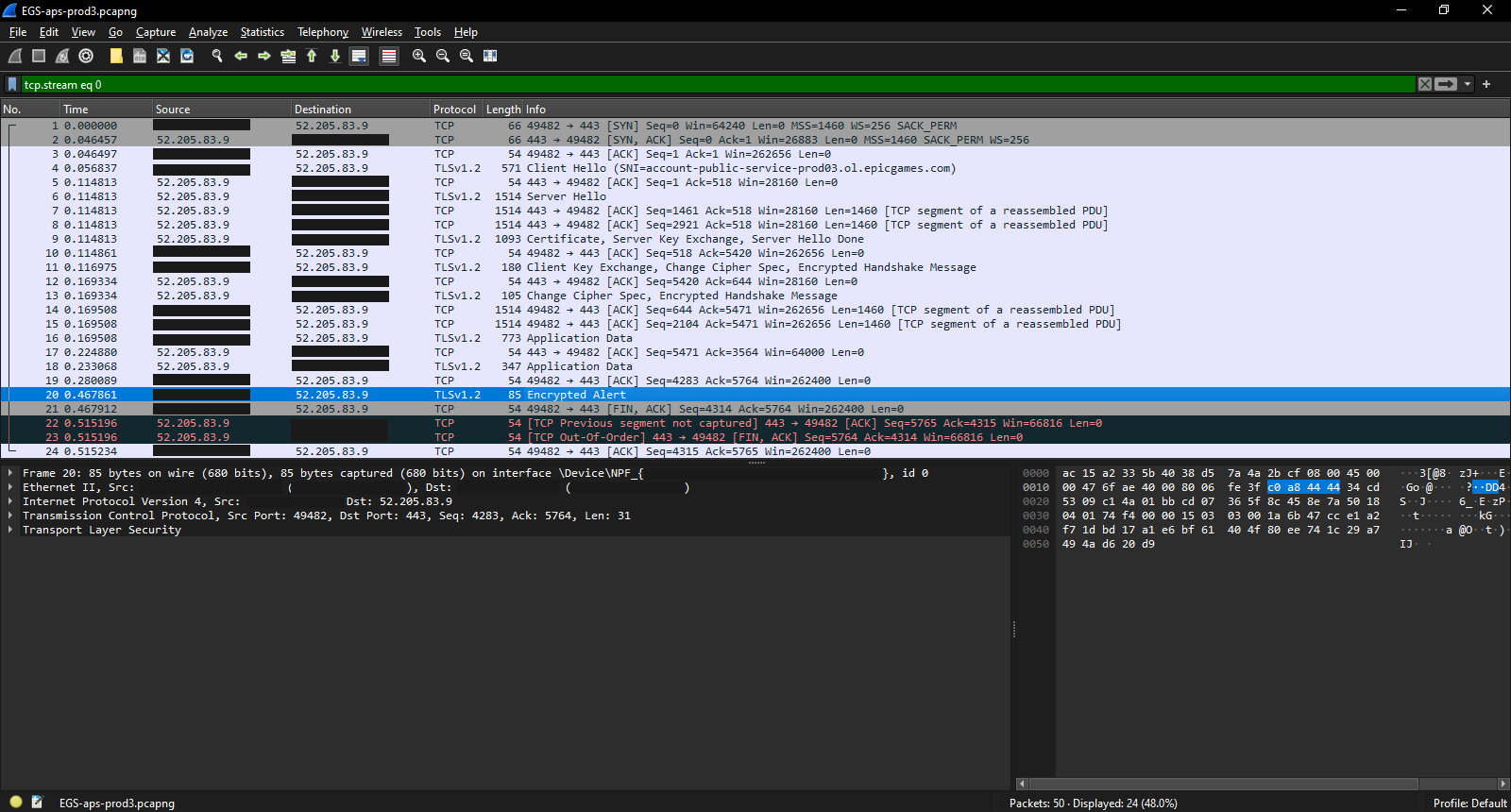
To make examining the data easier, I then ran a filter for ip.dst and ip.src using that address, before exporting that filtered data to a new PCAP file. The new PCAP was much smaller - surprisingly small, in fact.
A Short Handshake
With a total length of 50 packets, the exchange starts off with a TCP Handshake, which constitutes the first three packets. Then there's a client hello, with TLS 1.2 encapsulation, which renders a lot of the packet contents into unreadable gibberish.
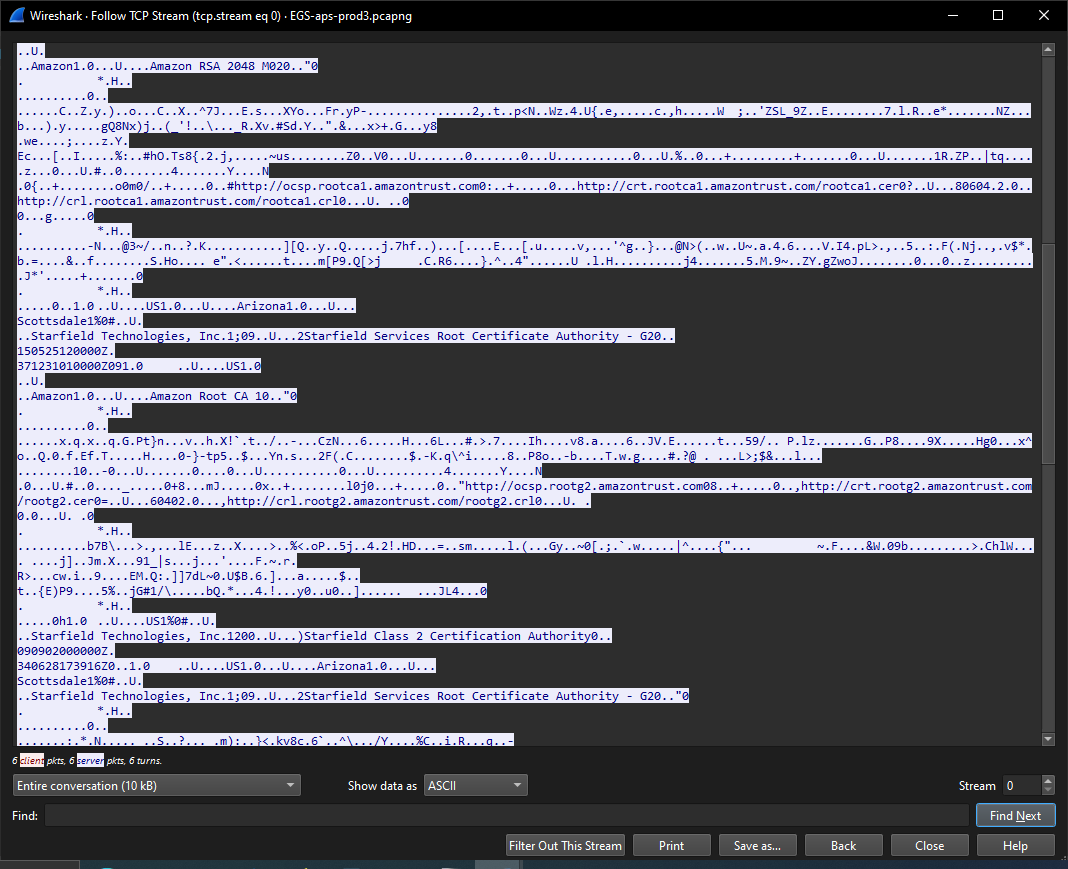
However, there are bits and pieces that can be gleaned from examining the TCP stream.
A Bunch of HTTP
One thing that stood out to me in the TCP stream was the number of visible HTTP addresses.
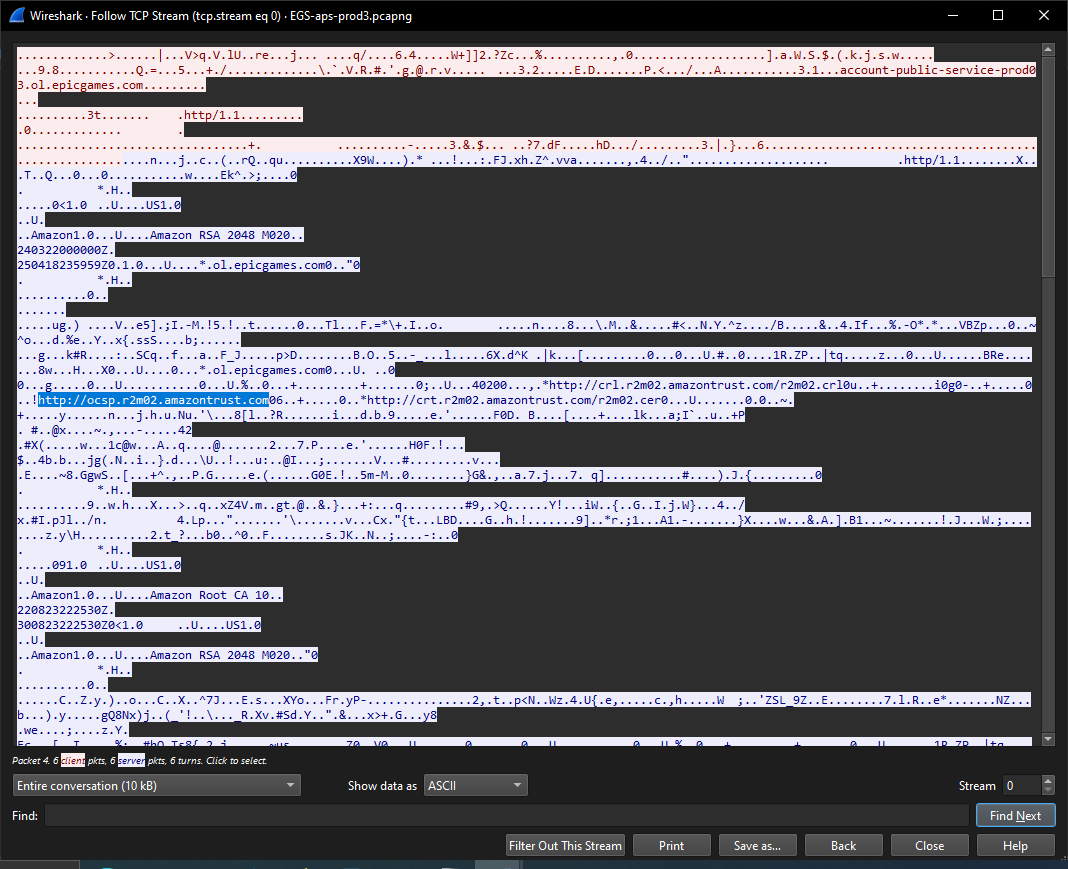
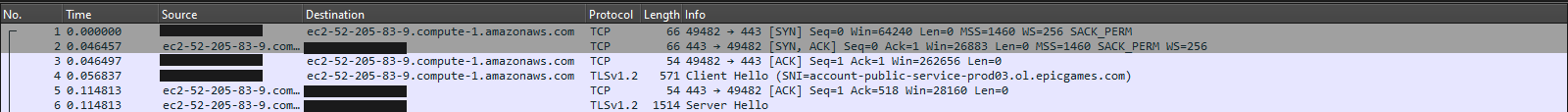
On one hand, the fact that they were Amazon addresses was not a surprise. Epic Games seems to use AWS infrastructure for all their online functionality. In fact, if you set Wireshark Name Resolution > Resolve Network Addresses, you get the following:
What did stand out to me was the use of HTTP in outwards facing URLs. Especially ones that could be accessed, to a limited degree, by non-Amazon individuals:
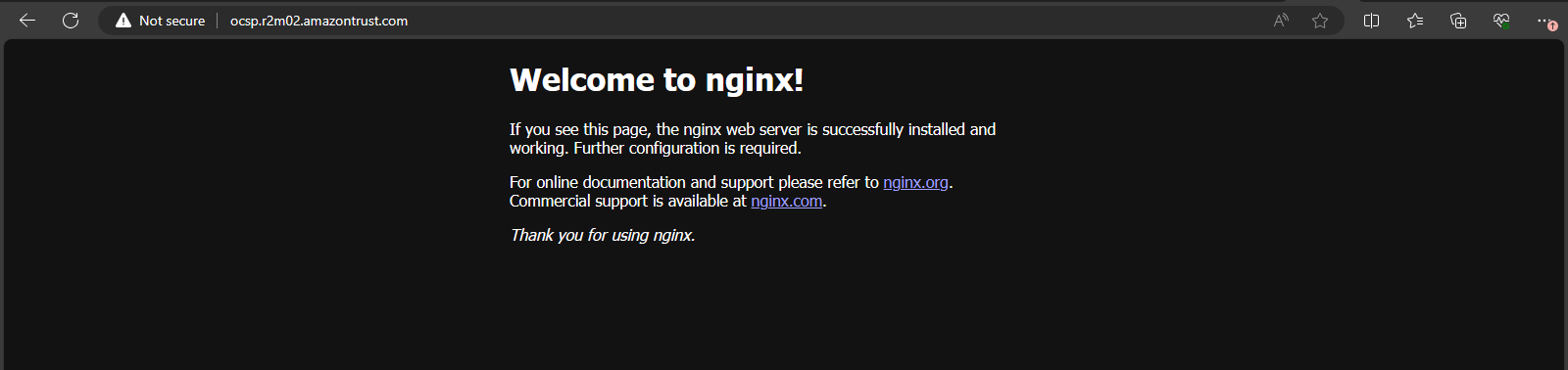
This might explain how Trojans wound up being distributed by this domain. It's entirely possible that malware was placed onto this server and distributed to other systems via the certificates, since they are automatically downloaded upon connection to the specified URL.
Other Interesting Tidbits
One interesting tidbit of information was that there's a root certificate authority operating out of Scottsdale, Arizona.
Starfield Technologies apparently provides the public key certificates for some of Amazon's web services. According to Amazon:
"Starfield Services Root Certificate Authority - G2" is an older root that is compatible with other older trust stores and clients that can not be updated. Including all five of the roots ensure maximum compatibility for your application.
Next Steps
Since there doesn't seem to be much traffic or anything really unusual going on with this IP address, it's time to look somewhere else.
The next IP address to check is going to the one associated with priceengine-ecomprod01-pub-2131700027.us-east-1.elb.amazonaws.c, which has a decent likelihood of generating a large volume of traffic. Will there be anything interesting to learn?

